(Prefer videos? Watch a brief summary of this article below.)
At 5:40 a.m., a contractor arrives to repair a packaging line. The night shift is leaving. A delivery truck is waiting at the gate. A production manager is asking why the line is still down.
In that rush, a weak entry process can become a safety risk, audit gap, or production delay. The wrong person enters the wrong zone. A visitor skips induction. A temporary badge stays active after the work is done.
That is why factory access control software is no longer just about opening doors. It is now a core part of manufacturing site security, daily operations, compliance, and emergency readiness.
At a Glance: What Factory Teams Should Know
- Entry is operational. It affects uptime, safety, audits, and response speed.
- Zones need different rules. A lobby, cleanroom, server room, loading dock, and hazardous area should not share the same logic.
- Contractors and visitors matter. Secure access systems for factories must manage non-employees with the same care as staff.
- Integration closes gaps. Visitor access software, badges, cameras, alarms, kiosks, and signage work better together.
- Cyber and physical risks now overlap. Physical entry, identity, and connected systems must be managed as one security environment.
Why Access Control Is Critical for Factories
Factory security has one difficult job: to protect people and production without slowing the plant down.
Growing risks and security needs in industrial environments
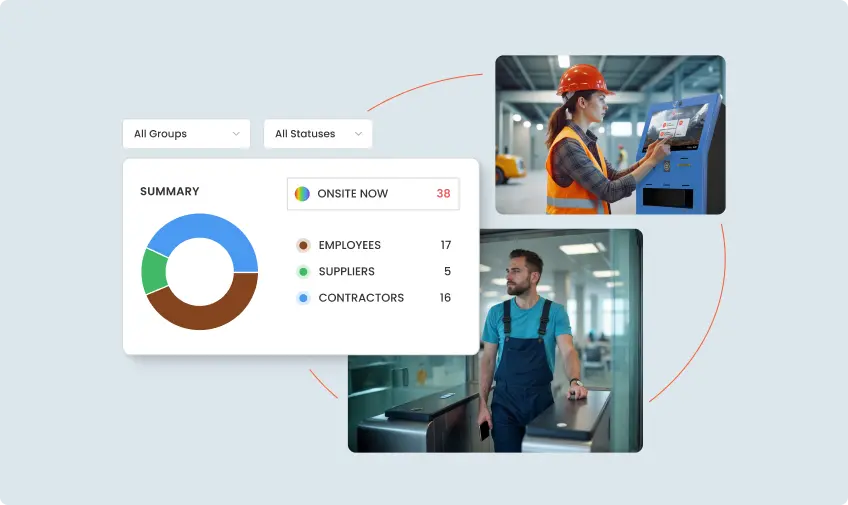
Manufacturing facilities are busy ecosystems. Employees, temporary workers, suppliers, inspectors, drivers, cleaners, and maintenance teams may all need to enter the site in a single day.
At the same time, industrial environments are more connected than before. Doors, badges, cameras, visitor systems, HR tools, and production networks often operate in the same operational space.
The Verizon 2025 DBIR Manufacturing Snapshot highlights how intrusion, social engineering, and application attacks remain serious risks for manufacturers. The ENISA Threat Landscape 2025 also underlines how the wider threat environment continues to evolve across Europe.
For factories, the message is clear. Physical entry and digital risk can no longer be treated as separate topics.
Protecting people, assets, and sensitive areas
A food manufacturer may need to keep guests away from allergen zones. An automotive plant may restrict prototype areas. A chemical facility may separate office traffic from hazardous storage.
Industrial facility access control makes these rules part of daily practice.
It answers practical questions:
- Who can enter this area?
- During which hours?
- With which approval?
- After which safety steps?
- For how long?
Good plant security software reduces guesswork. It helps guards, reception teams, and supervisors make consistent decisions, even during shift changes.
Compliance with safety and audit standards
Factories often need proof. Not just policy.
Access control compliance depends on reliable records. Access logs and tracking show who entered a zone, when they entered, whether entry was granted or denied, and which credential was used.
This matters after:
- Safety incidents
- Near misses
- Contamination events
- Lost badge reports
- Insurance reviews
- Internal and external audits
Paper logs rarely give enough detail. Digital records do.
What Is Access Control Software?
Before choosing a provider, define what the software must do. In a factory, security technology is not a stand-alone tool. It is part of the site’s operating rhythm.
Basic definition and role in physical security
Access control software manages who can enter buildings, rooms, gates, production zones, and restricted areas.
It connects people to permissions. Then it applies those permissions through doors, turnstiles, gates, elevators, lockers, or other entry points.
In industrial environments, access software for manufacturing supports security, safety, compliance, and workforce flow.
Key components: credentials, permissions, monitoring
Most systems include three basic layers:
- Credentials, such as badges, PINs, mobile passes, or biometrics.
- Permissions, such as role, department, zone, shift, and approval status.
- Monitoring, including dashboards, alerts, reports, and event logs.
Together, these layers create a controlled site environment.
The system should not only open the door. It should explain why the entry was allowed, denied, or escalated.
Types of access: biometric, RFID, PIN, mobile
Different facilities need different credential types.
RFID access control is common because badges are quick, familiar, and easy to issue. PINs can work for low-risk areas. Mobile credentials reduce plastic badge handling. Biometrics may be used in high-security areas where badge sharing is a concern.
The right choice depends on:
- Risk level
- Hygiene requirements
- Privacy rules
- Union considerations
- Worker volume
- Door traffic speed
A high-throughput factory entrance may need fast badge scanning. A sensitive lab may need stronger identity checks.
Connect visitor check-in, badges, approvals, and permission decisions before people reach the production floor.
Key Features to Look For
A factory is not an office with forklifts. The software must handle movement, urgency, and exception cases.
Real-time monitoring and alerts
Security teams need to see what is happening now.
If a door is forced open, a badge is denied repeatedly, or a contractor tries to enter the wrong zone, the system should trigger an alert immediately.
For example, if a refrigeration technician opens a door near a clean production line, security can respond before the incident becomes a shutdown.
Multi-location and multi-zone access configuration
Manufacturers often operate more than one site. Managing each plant separately creates confusion.
Multi-location access control lets teams set shared rules while adapting them to local layouts.
Zone-based access is especially important for:
- Production halls
- Warehouses
- Cleanrooms
- Machine cages
- Server rooms
- Loading bays
- Maintenance areas
- R&D spaces
This is where factory door access control becomes much more than a lock-and-key replacement.
Integration with video surveillance and alarm systems
Access events are more useful when connected to video and alarms.
A denied badge can pull up the matching camera clip. A forced door can trigger an alarm and notify the right team. A tailgating event can be reviewed with visual evidence.
This is how industrial security systems become practical. They connect signals that would otherwise sit in separate tools.
Cloud vs on-premises deployment
A cloud-based access system can support remote administration, faster updates, and easier scaling across sites.
On-premises deployment may suit plants with strict network separation, local control requirements, or specific data policies.
Many manufacturers choose a hybrid model. Door decisions stay local for continuity, while dashboards and administration run centrally.
Support for contractors and visitors
Contractor access permissions should be precise and temporary. A maintenance vendor may need entry to the boiler room from 7 a.m. to 1 p.m. on Friday. After that, the credential should stop working.
Visitor permissions should also connect to hosts, safety instructions, badges, and approved destinations.

Integration with Factory Operations
Entry control should not sit on the edge of operations. It should understand how the site actually works.
Connecting access software with visitor management
A visitor who signs in on paper is hard to track. A visitor who checks in digitally can be screened, approved, badged, instructed, and guided.
That journey matters at gates, docks, receptions, and contractor entrances.
Employee badge systems and time tracking
An employee badge system can support both building entry and attendance.
For example, operators may enter the production hall only during their assigned shift. Maintenance staff may enter a machine area only after a work order is approved.
This prevents early movement, reduces manual checks, and supports clearer accountability.
Shift-based access permissions
Shift scheduling integration is valuable in factories with rotating teams.
A badge can work for Monday’s night shift but not Tuesday’s day shift. Temporary workers can receive rights only for the hours they are assigned. Supervisors can receive broader permissions during handovers.
This keeps rules current without constant manual edits.
Emergency lockdown and mustering support
During a fire, chemical spill, intruder event, or serious machine incident, entry rules may need to change immediately.
Doors may lock, unlock, or switch behavior by area. Emergency teams need to know who is likely on site. Muster reports help account for employees, contractors, and visitors.
Evaluating Security Software Providers
Features matter. But the provider behind the platform matters just as much.
Vendor reliability and industry expertise
Ask whether the provider understands industrial workflows.
Factories have PPE rules, shift patterns, dock traffic, contractor tasks, noisy environments, and high-consequence zones. A generic office entry tool may not handle these realities well.
Look for experience with manufacturing, logistics, energy, healthcare, or other complex sites.
Scalability and future-proofing
Start with today’s doors. Then look ahead.
Will the platform support more sites, more visitor types, mobile credentials, self-service kiosks, badge printers, APIs, and advanced reporting?
The best security platform for manufacturers grows quietly in the background. It should not need to be rebuilt every time the plant changes.
Data protection and compliance standards
Data on access events is sensitive. It can reveal work schedules, movement patterns, host relationships, and sometimes biometric information.
Ask about:
- Encryption
- Data hosting
- Retention settings
- Administrator roles
- Audit logs
- User permissions
- Privacy controls
For cloud systems, confirm where data is stored and who can view it.
Support and maintenance services
A failed door system can disrupt production. Support cannot be an afterthought.
Check service levels, escalation paths, update practices, hardware replacement options, and administrator training.
Also, ask how integrations are maintained. A badge system connected to visitor management, HR, alarms, and cameras requires careful support over time.

Use Cases in Manufacturing Facilities
The strongest business case usually appears in everyday moments. Small improvements at the door can prevent large operational problems.
Access to hazardous zones and machinery
At a metal fabrication site, only trained employees should enter laser cutting areas. The software can check training status before granting entry.
No valid training record, no entry.
In a chemical plant, movement into storage zones may require role-based approval and additional safety acknowledgment.
Managing contractor access on site
Contractors often need temporary entry to specific areas.
A service technician may need the pump room today, but not the warehouse tomorrow. A cleaning crew may enter offices after hours, but not production zones.
Digital contractor permissions reduce badge misuse and help supervisors avoid awkward manual checks.
Real-time entry/exit logs for audits
A pharmaceutical manufacturer may need to prove who entered a controlled area during a batch run.
Real-time logs make that answer available in minutes. Paper sign-in sheets turn the same question into detective work.
Entry records also help during internal investigations, insurance claims, and compliance reviews.
Restricting movement during sensitive operations
Some factory moments require tighter control.
During a product launch, recall, quality hold, stock count, or high-value shipment, temporary restrictions may be needed.
Digital access management lets teams adjust movement rules without replacing locks or rewriting manual procedures.
Combine kiosks, visitor workflows, badges, and safety communication across your site.
Factory access control software is not about locking everything down. It is about letting the right people move confidently while keeping risk out of the blind spots. Choose a system that understands zones, shifts, visitors, contractors, audits, and emergencies. Then the platform becomes more than security. It becomes a calmer, faster, and safer way to run the plant.
FAQ
These are the questions factory teams usually ask before upgrading their systems.
Yes. Multi-site access software can manage shared policies across several plants while allowing local rules for each facility, building, zone, or department.
Visitor management verifies guests, captures required information, notifies hosts, issues badges, and can trigger door permissions. This creates a controlled flow from arrival to exit.
ROI comes from fewer manual checks, faster contractor processing, reduced audit work, lower incident risk, and less downtime caused by entry mistakes.
A cloud platform should use encryption, role-based administration, audit logs, retention controls, and secure hosting. Always confirm the provider’s security and compliance documentation.
Yes. Authorized administrators can usually update permissions remotely. They can revoke a lost badge, add a contractor, change zone rights, or respond to an emergency.