(Prefer videos? Watch a brief summary of this article below.)
A few years ago, access control was easy to overlook: a badge reader by the door, a spreadsheet at reception, a guard calling upstairs. Now it sits much closer to the heart of the business. One arrival can trigger identity checks, safety steps, notifications, permissions, and a clean audit trail in seconds.
That is why access control trends in 2026 feel bigger than hardware. They touch security, compliance, operations, and the everyday experience of being on site.
Key Takeaways
- Mobile access control is becoming the new normal for employees, contractors, and visitors.
- Biometric access systems are advancing, but privacy and governance now shape every serious rollout.
- AI access management is helping teams spot anomalies faster and automate routine decisions.
- Cloud-based access control is making secure multi-site access easier to manage and scale.
- Enterprise security integration now reaches into visitor management, HR, communications, and reporting.
- Smart locks and sensors are turning physical entry points into sources of real-time access analytics.
- The strongest systems in 2026 reduce friction without weakening compliance or control.
Overview of Access Control in 2026
The old question was simple: who gets through the door? The new question is broader and more useful.
Evolving role of access control in enterprise security
In 2026, access control is expected to do more than grant or deny entry. It is part of how companies verify identity, enforce policies, protect restricted areas, and keep records that stand up during an audit. For manufacturers and other complex sites, it also acts as an operational control layer connecting security, EHS, HR, and site leadership.
A real-life example makes the shift clear. Picture a contractor arriving at a factory at 6:45 a.m. Instead of waiting at a desk with paper forms, they scan a code, confirm site instructions, notify the host, and receive the proper permissions for the right zone. Same entrance. Much smarter process.
Market demand and compliance challenges
Business demand is moving in two directions at once. Leaders want less friction at the front door, but they also want more evidence behind the scenes. They need to know who entered, when, why, and under which rules.
Trend 1: Mobile-Based Access Systems
If there is one trend that feels unmistakably current, it is this one. The badge is no longer the star of the show.
Smartphone credentials and NFC tech
Mobile access control has moved from “nice to have” to a baseline expectation. Employees already carry a secure device. Businesses already need faster onboarding and easier revocation. Smartphone entry badges, NFC-based credentials, and wallet-style access flows answer both needs in one move. ENISA’s digital identity work points in the same direction, with strong emphasis on trusted digital identification and privacy-aware identity frameworks.
The business case is refreshingly practical:
- fewer lost cards
- faster credential updates
- cleaner temporary access for contractors
- less dependence on manual badge handling
Contactless entry for employees and visitors
Contactless security systems also improve the arrival experience. An employee taps in. A visitor preregisters from home. A truck driver checks in at the gate without making three phone calls or exchanging a clipboard. That kind of flow matters most when sites are busy, not when they are quiet.
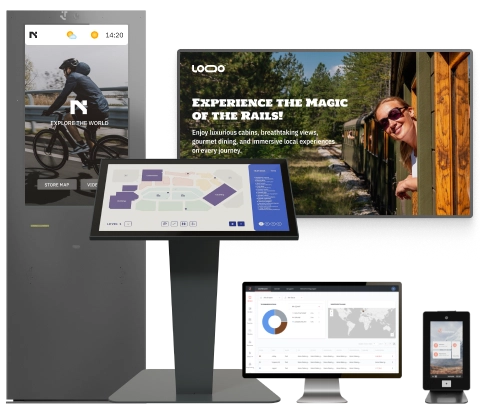
For businesses looking to connect entry with reception, badging, and guidance, a platform such as friendlyway helps turn entry into a single continuous journey rather than a patchwork of separate steps.
Connect visitor check-in, host alerts, badges, and wayfinding in one workflow.
Trend 2: Biometric Innovations
Biometrics still sparks strong opinions. For some buyers, they signal precision. For others, risk. Both instincts are reasonable.
Facial recognition and fingerprint scans
Biometric access systems can be powerful in high-security spaces where certainty matters more than convenience alone. Think healthcare zones, labs, data rooms, or government sites where shared credentials are a real concern. In those settings, facial recognition and fingerprint scans can add a valuable layer of digital identity verification.
Privacy, security, and ethical considerations
But this is where the conversation gets serious. The European Data Protection Board has stressed that biometric data, especially facial recognition, creates heightened risks for people’s rights and freedoms. Its statements underscore user control, privacy by design, and caution around centralized or excessive biometric processing.
That is why the strongest deployments are rarely biometric-only. More often, businesses use biometrics selectively, in limited zones, alongside other methods. It is not about chasing the flashiest technology. It is about matching assurance to actual risk.

Trend 3: AI and Machine Learning in Access Control
AI is quietly changing access control. Not with drama. With pattern recognition.
Behavior-based threat detection
AI access management helps security teams spot what humans often miss in a sea of events: repeated failed attempts, unusual entry times, access patterns that do not fit a person’s normal movement, or activity that jumps awkwardly between zones. In a multi-site organization, that kind of context matters because suspicious behavior rarely arrives labeled as suspicious.
Real-time access decisioning and automation
The payoff is speed. Low-risk arrivals move faster. Missing approvals can trigger instant blocks. Unusual events can be escalated without waiting for someone to notice them on a dashboard 20 minutes later. Good automation does not remove human judgment. It protects it by saving it for the moments that deserve attention.
Trend 4: Cloud-Based Access Management
This next trend is less flashy, but in many businesses it has the biggest operational impact. Cloud wins because complexity keeps growing.
Benefits of remote administration
Cloud-based access control makes it easier to manage permissions, policies, and reporting across locations without having to rebuild the same process five times. For multi-site businesses, that means more consistency and less drift between sites.
friendlyway’s platform offers cloud-based management across visitor, self-service, and workflow scenarios.
Cloud vs on-premises security trade-offs
On-premises systems still have their place. Some organizations need them. Some simply prefer them. But the decision is no longer about habit. It is about governance. Which model gives your team the clearest visibility, the strongest controls, and the least operational drag? In 2026, that question usually matters more than ideology.
Trend 5: Integration with Other Enterprise Systems
Access control becomes much more useful when it stops acting alone. That is when it starts earning a budget.
Connecting with visitor management and HR platforms
The most common integration scenarios are practical, not exotic. Visitor management. HR systems. Directory services. Host notifications. Compliance steps. A new hire should not wait days for access because the two systems do not talk to each other. A visitor should not have to repeat information that was already provided during preregistration.
friendlyway’s integration capabilities show how visitor and employee access, reporting, safety management, and communications increasingly operate as a single process.
Unified dashboards and real-time access logs
A unified view matters because modern security is rarely about one dramatic event. It is about patterns, exceptions, bottlenecks, and traceability. Real-time access analytics help teams answer basic but essential questions:
- Who is on site right now?
- Which zones are seeing unusual traffic?
- Where are approvals slowing people down?
- Which arrivals still need action?

Trend 6: IoT and Smart Hardware
Hardware is getting smarter, yes. More importantly, it is getting more talkative.
Smart locks, sensors, and occupancy tracking
Smart locks and sensors, kiosks, readers, and IoT-enabled door systems now provide signals that go well beyond “open” or “closed”. They can support occupancy tracking, reveal doors that are repeatedly propped open, and give teams better visibility into how people move through a site. In modern building access systems, this turns physical infrastructure into operational intelligence.
Energy efficiency and environmental data
There is a quieter upside, too. Occupancy-linked data can help buildings respond more intelligently with lighting, room activation, or environmental controls. Security leaders are increasingly asked to show broader business value. Systems that support both protection and efficiency are easier to defend in the boardroom.
Trend 7: Regulatory and Compliance Considerations
Every access project eventually reaches the same moment. The technology works. Now prove it is governed.
GDPR, OSHA, and other data protection requirements
For European organizations, GDPR remains central, especially when access workflows involve personal identity data or biometrics. ENISA continues to stress the connection between digital identity, privacy, and cybersecurity. For global businesses, safety obligations add another layer, particularly when accurate records of who is on site become critical during emergencies.
Secure logging and audit trails
This is where compliance-ready access control earns its keep. Clean logs. Time-stamped actions. Signed acknowledgements. Defensible retention policies. Paper logbooks and email chains do not scale well, and they rarely help in a serious audit. Digital workflows do.
Emerging Use Cases
The market is expanding fastest where entry is messy, urgent, or high-stakes. That is where old systems show their age.
Access control in hybrid workplaces
Hybrid workplace access now needs flexibility by default. Staff come in less predictably. Guests arrive for shorter visits. Teams use shared spaces differently. Static permissions and legacy badge processes feel clumsy in that environment.
Logistics and supply chain applications
Logistics is a different beast altogether. Speed matters. So does traceability. Drivers, vendors, temporary workers, and contractors can all arrive inside the same half-hour window. In those moments, digital flows are not a luxury. They are the only way to stay fast without losing control.
High-security government and healthcare sites
At the other end of the spectrum, government and healthcare environments still need layered controls and stronger proof of identity. Here, the best systems are strict without becoming exhausting. That balance is harder than it sounds.

Choosing the Right Access Control Solution
The shortlist should not begin with devices. It should begin with fit.
Scalability, integrations, and vendor support
A strong solution should handle growth, support enterprise security integration, and adapt to different sites without forcing the same workflow everywhere. It should be just as comfortable in a polished office lobby as it is at a busy plant gate.
Cost, TCO, and ROI considerations
The cheapest product on paper can become the most expensive in real life. Total cost of ownership includes admin time, badge management, manual exceptions, compliance effort, and the cost of a poor visitor experience. The better investment usually feels simpler day-to-day. That is a useful test.
See how friendlyway supports secure, connected journeys across sites, teams, and visitor types.
The direction of travel is clear. Access control 2026 is more mobile, more connected, more data-aware, and far less tolerant of friction. The organizations that come out ahead will not be the ones with the most hardware. They will be the ones who design entry as a living business process: secure, human, and scalable.
FAQ
There is no single winner for every site. In practice, the strongest setup is usually layered: mobile credentials or badges for everyday access, role-based permissions underneath, and biometrics reserved for higher-risk areas.
AI helps security teams filter noise, spot unusual behavior, and automate routine decisions. It does not replace policy. It makes policy enforcement easier and faster.
They can be very safe when governance is strong. Clear admin roles, secure integrations, reliable logging, and good configuration discipline matter more than the hosting label alone.
Yes. In fact, that is one of the clearest reasons businesses adopt modern platforms. Centralized control with local flexibility is now a major advantage.
The most common scenarios include visitor management, HR systems, directory services, host notifications, compliance workflows, and reporting dashboards.