(Prefer videos? Watch a brief summary of this article below.)
Key Takeaways
- Industrial visitor control should start before arrival, not at the gate.
- Different visitor types need different checks, badges, and access rights.
- Strong access management improves safety, compliance, and flow.
- Digital tools reduce manual errors and create reliable entry and exit logs.
- The best systems integrate check-in, badging, zoning, and audit trails into a single process.
The weakest point in many industrial facilities is not the perimeter fence. It is the moment a visitor shows up, and nobody is fully sure who they are, where they should go, what they may access, or whether they understand the risks around them. In a factory, warehouse, utility site, or processing plant, that gap can quickly become a safety issue.
That is why visitor access management has moved far beyond the reception desk. Today, it is part of industrial site security, operational continuity, and compliance. For manufacturers with suppliers, auditors, contractors, and temporary workers moving in and out every day, the right process protects people without slowing the business down.
Why Visitor Access Management Matters in Industrial Sites
In industrial environments, a visitor policy is never just an admin task. It is a risk-control measure.
Unique risks in industrial environments
Visitor management in factories is more challenging than in office settings because the risks differ. Heavy machinery, forklifts, restricted production zones, hazardous materials, and confidential processes all raise the stakes.
A missed sign-in, an unclear escort rule, or weak visitor screening procedures can expose the site to injury, theft, unplanned downtime, or IP loss. Good manufacturing visitor policies reduce uncertainty before it turns into an incident.
Legal and compliance requirements
Industrial operators often have to align with local health and safety law, internal site rules, customer requirements, and industry frameworks. OSHA guidance, for example, emphasizes that safety commitments should be communicated not only to workers but also to contractors, suppliers, and visitors.
Globally, ISO 45001 also shapes how many businesses structure occupational health and safety management. It provides a framework for managing OH&S risks and improving performance, which makes controlled visitor entry a natural part of a broader safety system.
Impact on operations and safety
Poor factory visitor check-in does more than create queues. It distracts reception and supervisors, creates blind spots during emergencies, and makes audits harder than they need to be.
A clean process does the opposite. It gives teams secure facility access, faster approvals, and a live record of who is on site and why.
Automate pre-registration, safety acknowledgments, badging, and approvals with friendlyway’s visitor management solution.
Preparing for Visitor Entry
The best arrival experience is prepared before the visitor reaches the facility.
Pre-registration and vetting
Pre-registration enables sites to verify visit purpose, host, timing, and required documents in advance. Modern systems can send email invitations, collect data before arrival, and allow visitors or contractors to complete check-in quickly with a QR code or confirmation number.
For higher-risk visits, vetting should also cover NDAs, work permits, insurance evidence, training status, and watchlist checks where appropriate. This is especially important in a contractor access system used across multiple plants or shifts.
Communicating safety protocols in advance
Do not wait until the lobby to explain the rules. Send visitor safety protocols before arrival so guests know the PPE rules, photography restrictions, parking instructions, and what to do in an emergency.
This cuts friction at the front desk and improves compliance. It also sets the tone: safety starts before entry, not after.
Defining visitor categories (suppliers, auditors, contractors)
Not every guest belongs in the same workflow. A supplier making a dock delivery should not move through the same path as an auditor or a contractor working near production equipment.
Use clear categories, then map each one to default permissions, required documents, and escort rules. That is where industrial visitor control becomes consistent instead of improvised.
| Visitor type | Main concern | Required checks | Default access rule |
|---|---|---|---|
| Supplier/delivery driver | Traffic flow, misrouting, yard safety | Delivery reference, ID check, site notice | Yard or dock only |
| Auditor/inspector | Sensitive data, restricted zones | Appointment, host approval, NDA if needed | Escorted, time-limited access |
| Contractor/temp worker | Hazard exposure, permit compliance | Training proof, PPE acknowledgment, permit review | Role-based zone access |
| Customer/partner | Safety and IP protection | Host approval, ID check, confidentiality notice | Meeting areas or escorted route |
On-Site Access Control Procedures
Once a visitor arrives, the process should be fast, visible, and hard to bypass.
Secure check-in and identity verification
A secure check-in flow should confirm identity, match the visit against a planned booking, and log the time of entry. A modern visitor management system can support pre-registration, identity verification, watchlist checks, and real-time tracking of visitor access and movements.
That matters for both safety and trust. The site knows who entered. The host knows they arrived. The visitor knows the process is controlled.
Badge issuance and access level assignment
Badges should show more than a name. They should reflect role, validity window, host, and access level. In industrial settings, contractor badge issuance often becomes the bridge between check-in and the plant access control system.
friendlyway’s manufacturing and visitor tools support temporary badges, RFID cards, identity verification, and zone- or role-based restrictions, which are exactly the kinds of access control best practices industrial sites need.
Briefing visitors on safety and evacuation plans
Every visitor needs a safety briefing for guests that matches the site’s real risk. Some visits may need a short acknowledgment. Others need a full induction.
Emergency planning is part of that. OSHA’s evacuation guidance notes that visitors should be accounted for after an evacuation and may need help exiting, which is one reason reliable sign-in lists and host responsibility matter so much.
Access Zone Management
After check-in, access should narrow, not open up.
Role-based and location-based restrictions
The safest rule is simple: give visitors the least access needed for the task. Not more. Role-based permissions and visitor zoning restrictions reduce unnecessary exposure to high-risk areas.
That makes access easier to defend during audits and easier to understand for staff on the ground.
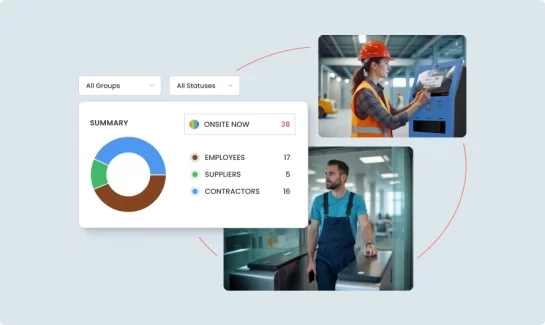
Real-time location awareness and tracking
Visitor tracking software becomes especially valuable when a site is large, multi-building, or shift-based. Security teams need to know who is on site, where they should be, and whether they have overstayed their approved window.
Real-time visitor location and reporting are already part of modern digital platforms, which is why manual sign-in books feel increasingly out of place in industrial settings.
High-risk areas need more than signs on doors. They need enforced rules tied to credentials, turnstiles, barriers, or escorted workflows.
That is where integrations matter. Contractors complete safety forms at a kiosk and, once approved, the system triggers an integrated turnstile or barrier to open and records the event.
Integrating Technology for Efficiency
Good process design matters. Good technology makes it scale.
Visitor Management Systems (VMS)
A strong VMS brings visitor access management into one controlled flow: invitations, check-in, document signing, badging, notifications, and reporting. It also helps standardize visitor management across factories.
If you are comparing tools, look for configurable workflows, digital signatures, pre-registration, and support for different visitor journeys. That is where a platform stops being a digital guestbook and starts becoming infrastructure.
Integration with access control, CCTV, and HR systems
A standalone tool can help, but an integrated one does more. When visitor data connects with access control, calendars, HR records, and notifications, approvals happen faster, and fewer manual steps fall through the cracks.
friendlyway’s integrations include workflows such as QR-based arrivals, host notifications in Teams, and connected gates or barriers for industrial access scenarios.
Cloud-based dashboards and audit trails
Cloud dashboards help security, reception, and site managers work from the same source of truth. That matters for entry and exit logs, exception handling, and post-incident review.
It also supports audit readiness. friendlyway’s solutions include visitor logs, reporting, safety management, and customizable workflows for production environments.
Post-Visit Procedures and Data Retention
Access control does not end when the meeting does.
Visitor sign-out and return of credentials
A clean sign-out process confirms the visitor has left, closes the visit record, and ensures credentials are returned or deactivated. This sounds basic, but it is where many sites still lose control.
If a badge remains active after departure, the site has a gap. If the person is still listed as present during an evacuation, the site has confusion.
Storing access data for audit readiness
Retention should be purposeful. Keep the access data you need for legal, operational, or audit reasons, and document why you keep it.
Digital systems make this far easier than paper folders. They also reduce the risk of missing forms, unreadable handwriting, or scattered files.
Analyzing visit patterns for operational improvement
The best teams do not just store logs. They learn from them. Visit peaks, repeat contractor traffic, dwell times, and denied access attempts can all show where process design needs work.
That is how visitor access management becomes a source of operational insight, not just a compliance function.
Compliance and Standards Alignment
Compliance works best when it is built into the workflow instead of bolted on later.
OSHA, ISO 45001, and industry-specific regulations
For global businesses, the exact rulebook varies by region and sector. The principle remains the same: identify risks, control access, document actions, and prepare for emergencies.
A practical visitor and contractor management setup supports that by capturing required forms, acknowledgments, and visit data in one place. It involves digital document signing, QR-based arrivals, and configurable workflows that help align site processes with internal and external requirements.
Documentation and reporting best practices
Documentation should be structured, searchable, and tied to the visit record. That includes approvals, timestamps, signed policies, host details, and exceptions.
This is one reason paper-based systems struggle during audits. They create effort. Digital reporting creates evidence.
GDPR and data protection measures
If your business processes visitor data from people in the EU, GDPR matters even if your company is based elsewhere. Keep data collection minimal, define retention periods, and make privacy notices easy to access.
Be extra careful with biometrics. EU guidance treats biometric data used to uniquely identify a person as sensitive data, which means stricter conditions apply. For many industrial sites, QR codes, photo badges, RFID, and escorted access are enough without adding that complexity.
Common Mistakes to Avoid
Even well-run sites repeat the same errors.
Lack of role-based permissions
One badge type for everyone is a weak policy. Different people need different levels of access, time windows, and supervision.
Manual tracking systems
Paper logs and spreadsheets still exist, but they are slow, fragile, and hard to audit. They also make monitoring temporary workers much harder than it should be.
Ignoring temporary/contractor risks
Contractors often spend more time in operational zones than occasional guests. Treating them as “just visitors” is a common mistake.
A stronger model combines pre-screening, contractor badge issuance, role-based access, and reliable sign-out. The result is tighter industrial site security without creating an unfriendly arrival experience.
Explore how friendlyway’s manufacturing solutions combine visitor workflows, access control, reporting, and safety management for complex sites.
Modern visitor access is not about adding friction. It is about putting the right checks in the right places so people can move safely, confidently, and with clear accountability. When industrial facilities combine pre-registration, secure check-in, zone-based permissions, visitor-tracking software, and disciplined data handling, they do more than protect the gate. They protect the operation.
FAQ
Yes. Many sites now use self-service kiosks, pre-registration, automated badge printing, and host notifications to manage arrivals with less reliance on the front desk. friendlyway’s platform and integration workflows support that model, including QR-based check-in and notifications to hosts.
A VMS creates structured records: who entered, when they arrived, what they signed, which badge they received, and when they left. That makes audits faster because entry and exit logs, visitor acknowledgments, and reporting are already organized.
Usually not. It can make sense for very high-security areas, but many plants achieve strong control with identity checks, photo badges, QR codes, RFID, escort rules, and time-limited access. If biometrics are used, data protection requirements become more demanding.
Any industry with safety risks, restricted areas, sensitive processes, or frequent third-party traffic benefits. That includes manufacturing, logistics, energy, chemicals, construction, critical infrastructure, and regulated production sites.
Keep the process clear, fast, and relevant. Ask only for the information you need. Send instructions in advance. Make wayfinding simple. And ensure the system adapts to the visitor type rather than forcing every guest through the same journey.