Secure Access Control for Critical Infrastructure Operators
Implement reliable, audit-ready access solutions for critical facilities, aligned with national and global standards for security, compliance, and physical resilience.

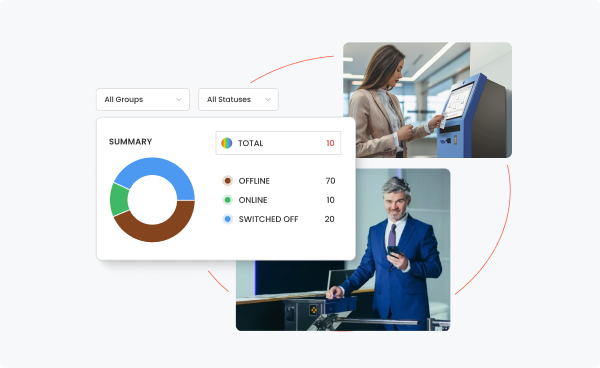
End-to-End Access Control
A modern access control system for utilities, municipal providers, hospitals, and other critical entities combines digital visitor management, physical access control, and IT integrations to create a seamless and efficient access process.

Strengthen Physical Resilience
Meeting regulatory expectations for physical resilience takes more than basic access checks. friendlyway supports operators in protecting sites, buildings, and people.
Ensure Compliance
With friendlyway, you meet the requirements of the CER Directive and ISO 27001 — from protection needs assessment through audit-proof implementation.
Check in here for a free demo and consultation
Submit the contact form and a friendlyway team member will reach out shortly.

FAQ
What does the CER Directive mean for critical infrastructure operators?
CER requires operators to strengthen physical resilience — among other things, through access systems, risk management, and complete, traceable logging.
What types of systems improve physical resilience?
Access control, video surveillance, fire protection, anti-sabotage measures, emergency plans, and structural safeguards.
How long does implementation take?
Typically 2–8 weeks, depending on complexity, number of sites, and required hardware.
Which standards must be met?
friendlyway solutions are designed to comply with international security and data protection standards, including ISO 27001 and GDPR. We also ensure alignment with local and global industry regulations for critical infrastructure (e.g., the German IT Security Act 3.0), providing robust, audit-ready access control solutions.
What does a security audit usually look like?
A security audit typically includes four steps:
- Document review: Access logs, risk analyses, emergency concepts
- On-site inspection: Terminals, entry portals, redundancy systems
- Test scenarios: Simulated outages (e.g., power/system) and validation of backup/lockout procedures
- Audit report: Findings, risk assessment, and recommended actions



